WordPress pharma hack, also known as Japanese or Chinese keywords hack. Hacker uses WordPress vulnerabilities and manipulates website SEO meta content such as page title and description to sell/promote illegal drugs. Typically pharma hack is not visible on web pages for direct visitors. But when the website is searched on Google, it displays infected pages of Japanese characters. Mainly attackers target vulnerable WordPress websites with vulnerable themes and plugins to inject files besides creating a backdoor inside the database, plugins, and themes.
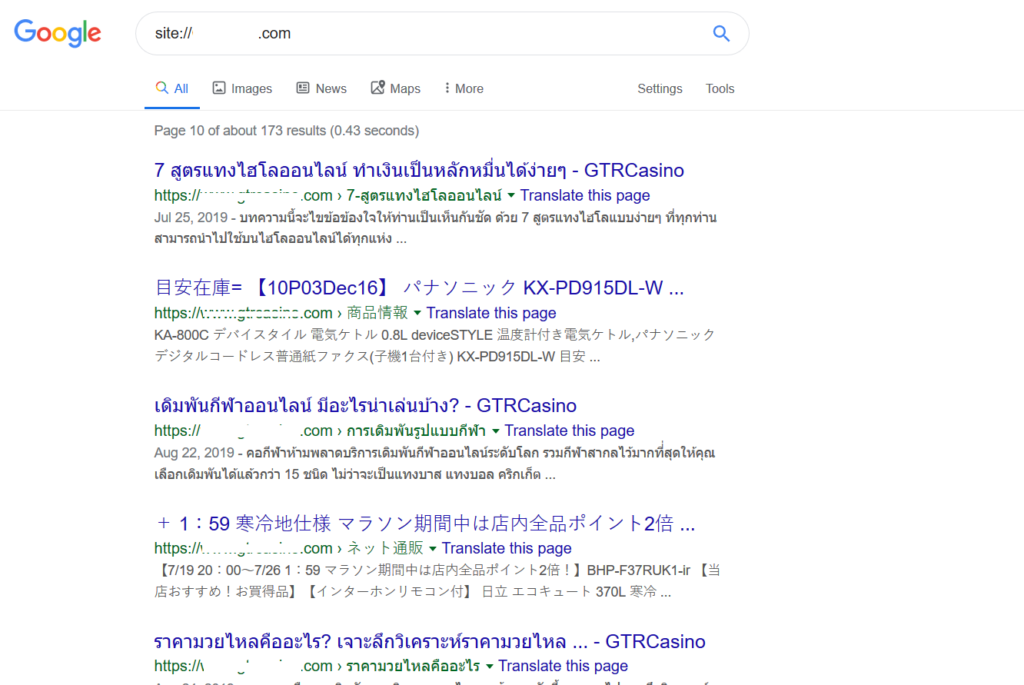
Identify pharma hack using google search
If your website is a victim of this hack, you probably know by noticing Google search results. You can check Google indexed pages by typing site:yourwebsite.com
You will get something like this image below.
Hackers also may inject affiliate links to promote their products. In that case, search engine visitors will be redirected to a different spammy website.
Some WordPress pharma hack exploits
Identifying the root of a pharma hack is not so easy. Hackers can use different injection techniques based on disclosed vulnerabilities to get what they want.
Website file modification
In these cases, attackers target vulnerable WordPress websites where file modification is possible using WordPress core, theme, or plugin vulnerability. The attacker tries to inject malicious scripts into a plugin, theme, or WordPress core file. Sometimes it remains hidden or unknown for months. Some common files we found in different cases are:
wp-content/uploads/.*php (random PHP name file)
wp-content/wp-update.php
wp-content/themes/index.php
wp-includes/images/wp-img.php
Some piece of code we found in those files:
Malicious scripts in database
In this case, we found malicious scripts hidden into WordPress database tables.
Most targeted tables are:
wp_options
wp_posts
wp_postsmeta
Some table row data found as:
wp-options > class_generic_support
wp-options > widget_generic_support
wp-options > wp_check_hash
wp-options > rss_7988287cd8f4f531c6b94fbdbc4e1caf
wp-options > rss_d77ee8bfba87fa91cd91469a5ba5abea
wp-options > rss_552afe0001e673901a9f2caebdd3141d
Backdoor admin